Your cart is currently empty.








Watch
Course PreviewLearning Format
Online Bootcamp
Live Classes
11 Months
Executive PG
Certification
Campus Immersion
iHUB, IIT Roorkee
EMI Starts
at ₹7376/month*
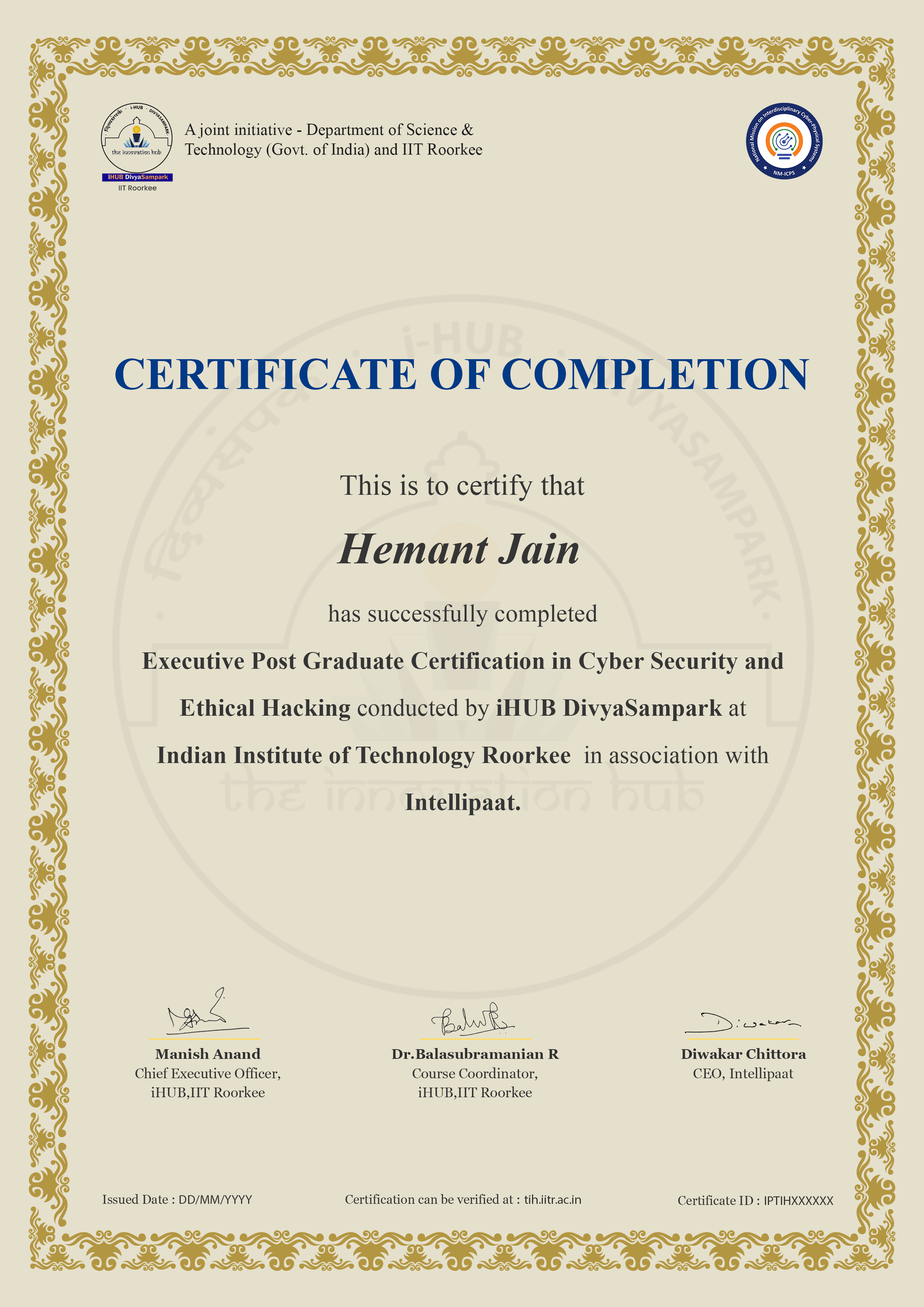
This Executive Post Graduate Certification Program in Ethical Hacking by iHUB DivyaSampark, IIT Roorkee, offers 10 modules and a career-accelerating capstone project to elevate your professional journey. This course will help you gain expertise in Networks, SOC, Application Security, Risk Analysis, and Mitigation via live classes by Industry Expert and master classes by IIT faculty.
About iHUB DivyaSampark, IIT Roorkee
iHUB DivyaSampark at IIT Roorkee, established under the National Mission on Interdisciplinary Cyber-Physical Systems (NM-ICPS) by the Department of Science and Technology (DST), focuses on fostering innovation in advanced technologies such as AI, ML, and more. The hub plays a pivotal role in technology development, incubation, and startups, particularly in areas like Healthcare,Read More..
Upon the completion of this program, you will receive:
About the EC-Council
This American organization offers education, training, and services on ethical hacking. The certification by the EC-Council validates the various ethical hacking skills that the learners will be trained in through the program.
Benefits for students from EC-Council
The CISO is responsible for overseeing the organization’s overall cybersecurity strategy and ensuring the implementation of effective security measures. They develop policies, manage risk, and lead incident response efforts.
Security analysts monitor and analyze systems, networks, and applications for potential security threats. They investigate security incidents, perform risk assessments, and implement security controls to protect company assets.
Security engineers design and implement security solutions, including firewalls, encryption systems, and intrusion detection systems. They conduct vulnerability assessments, develop secure architectures, and respond to security incidents.
Network administrators manage and maintain the organization’s computer networks. They configure network devices, monitor network performance, and implement security measures to protect against unauthorized access.
Security architects design and develop security frameworks, policies, and procedures for the organization. They collaborate with stakeholders to define security requirements and ensure that systems are designed with security in mind.
SOC analysts monitor the organization’s systems and networks for security events, triage incidents, and escalate as needed. They analyze security logs, investigate potential threats, and provide real-time responses to security incidents.
Skills to Master
Ethical Hacking
Cryptography
Cyber Security
Networks
Application Security
Risk Analysis and Mitigation
Tools to Master
1.1 Introduction to Linux OS fundamentals
1.2 Linux Basics – file handling, data extraction, etc.
1.3 Hands-on-Sessions and assignments for practice purpose
2.1 Networking basics- Switches, routers, and wireless access points
3.1 Introduction to Kali Linux
3.2 Services in Kali (HTTP, SSH)
3.3 Command-line utilities (Wget, curl, grep, awk, and many more)
3.4 Key concepts and basics of scripting (Piping, Redirection and Bash Scripting)
3.5 Tools and utilities in Kali Linux ( Netcat, Socat, Powercat, Powershell, etc.)
4.1 Introduction to Ethical Hacking
4.2 Footprinting and Reconnaissance
4.3 Scanning Networks
4.4 Enumeration
4.5 Vulnerability Analysis
4.6 System Hacking
4.7 Malware Threats
4.8 Sniffing
4.9 Social Engineering
4.10 Denial-of-Service
4.11 Session Hijacking
4.12 Evading IDS, Firewalls, and Honeypots
4.13 Hacking Web Servers
4.14 Hacking Web Applications
4.15 SQL Injection
4.16 Hacking Wireless Networks
4.17 Hacking Mobile Platforms
4.18 IoT and OT Hacking
4.19 Cloud Computing
4.20 Cryptography
4.21 Working with Kali Linux 2021.1
5.1 Basics of Static and Dynamic Analysis
5.2 Virus Detection Methods
5.3 Fileless Malware Analysis
5.4 AI-based Malware Analysis
5.5 Advance Analysis
6.1 Domain One – Security and Risk Management
6.2 Domain Two – Asset Security
6.3 Domain Three – Security Architecture and Engineering
6.4 Domain Four – Communication and Network Security
6.5 Domain Five – Identity and Access Management (IAM)
6.6 Domain Six – Security Assessment and Testing
6.7 Domain Seven – Security Operations
6.8 Domain Eight – Software Development Security
7.1 SecOps: Protecting, Managing, responding and Monitoring
7.2 Cyber Security threat intelligence salary
7.3 Security data management – Event Logging
7.4 Improved Identification of Incidents using Threat Intelligence
7.5 Incident Response
8.1 Overview of Azure Security
8.2 Active Directory (AD) of Azure for Workloads
8.3 Network Security for the Protection of the Platform
8.4 Host Security for the Protection of the Platform
8.5 Security and Containers
8.6 Role-based Access Control (RBAC) and Security Operations
8.7 Data Services Security
8.8 Security of Storage
This module will teach you how to safeguard a web application against being hacked, along with key considerations when making an app secure. Your capstone project will give you exposure to both sides, giving an understanding of both working environments.
10.1 Introduction to Generative AI in Cybersecurity
10.2 Generative AI vs. traditional AI in cyber defense
10.3 Threat Detection and Analysis with Generative AI
10.4 AI-driven pattern recognition in cyber threats
10.5 Generative AI for identifying system vulnerabilities
10.6 AI-driven decision-making in cybersecurity incidents
10.7 Monitoring user behavior patterns to detect anomalies
10.8 AI-Driven Risk Management and Compliance Monitoring
10.9 Ethical Considerations of AI in Cybersecurity
10.10 The Future of Generative AI in Cybersecurity
11.1 Introduction to Python and IDEs
11.2 Python Basics
Learn all these concepts along with real time hands on sessions and practice assignments.
All the projects included in this program are aligned with the industry demands and standards. These industry-oriented projects will test your level of knowledge in the Ethical Hacking domain and also help you get exposure to real-life scenarios.
Practice 20+ Essential Tools
Designed by Industry Experts
Get Real-world Experience

Admission Details
The application process consists of three simple steps. An offer of admission will be made to selected candidates based on the feedback from the interview panel. The selected candidates will be notified over email and phone, and they can block their seats through the payment of the admission fee.
Submit Application
Tell us a bit about yourself and why you want to join this program
Application Review
An admission panel will shortlist candidates based on their application
Admission
Selected candidates will be notified within 1–2 weeks
Total Admission Fee
EMI Starts at
We partnered with financing companies to provide very competitive finance options at 0% interest rate
Financing Partners
![]()
Admissions close once the required number of students is enrolled for the upcoming cohort. Apply early to secure your seat.
Next Cohorts
| Date | Time | Batch Type | |
|---|---|---|---|
| Program Induction | 4th April 2026 | 08:00 PM - 11:00 PM IST | Weekend (Sat-Sun) |
| Regular Classes | 4th April 2026 | 08:00 PM - 11:00 PM IST | Weekend (Sat-Sun) |
The program provides a holistic education in ethical hacking. The advanced certification offered by iHUB DivyaSampark, IIT Roorkee is aligned with industry requirements and will enable you to interview with leading MNCs.
Intellipaat provides career services that include guaranteed interviews for all learners enrolled in this course. iHUB DivyaSampark, IIT Roorkee is not responsible for career services.
You will be taught by the best practitioners in the industry and the course has been developed in consultation with IIT faculty.
If you miss a live class, you will receive the recording of the class within the next 12 hours. If you need assistance, you’ll also have access to our 24/7 support team to help you with any questions you may have.
To complete this program, it is recommended that you spend approximately 6-8 hours per week studying.
Yes. You may contact course advisors to learn more about scholarship opportunities.
This advanced certification program is conducted online for 11 months and is accompanied by several live sessions with instructors.
To be included in the placement pool, the learner must complete the course and submit all projects and assignments. He/she must then pass the PRT (Placement Readiness Test) to be accepted into the placement pool and gain access to our job portal and career mentoring sessions.
All candidates applying for this course are eligible for equity-based seed funding and incubation support from iHUB DivyaSampark, IIT Roorkee, for their startup ideas. Enrolled students will have the opportunity to pitch their ideas to the iHUB DivyaSampark team, and shortlisted proposals may receive funding of up to ₹50 lakh, along with full incubation support.
Additionally, candidates who are currently enrolled in a degree program and have their startup idea approved may also receive a monthly fellowship/scholarship of ₹8,000 during the early phase of their project to encourage and support innovation.
This Executive Post Graduate Certification in Ethical Hacking will help you pass the Certified Ethical Hacker Certification for CEH v12, Certified Information System Security Professional Certification & Microsoft Certified: Azure Security Engineer Associate (Exam AZ 500).
Please note that the course fees is non-refundable and we will be at every step with you for your upskilling and professional growth needs.
Due to any reason you want to defer the batch or restart the classes in a new batch then you need to send the batch defer request on [email protected] and only 1 time batch defer request is allowed without any additional cost.
Learners can request for batch deferral to any of the cohorts starting in the next 3-6 months from the start date of the initial batch in which the student was originally enrolled for. Batch deferral requests are accepted only once but you should not have completed more than 20% of the program. If you want to defer the batch 2nd time then you need to pay batch defer fees which is equal to 10% of the total course fees paid for the program + Taxes.
Yes, Intellipaat certification is highly recognized in the industry. Our alumni work in more than 10,000 corporations and startups, which is a testament that our programs are industry-aligned and well-recognized. Additionally, the Intellipaat program is in partnership with the National Skill Development Corporation (NSDC), which further validates its credibility. Learners will get an NSDC certificate along with Intellipaat certificate for the programs they enroll in.
The total duration of the program is 11 months and out of which 2 months will be for project work.
What is included in this course?
 Click to Zoom
Click to Zoom
 Click to Zoom
Click to Zoom