Your cart is currently empty.







This PG certification in Cyber Security & Ethical Hacking by E&ICT Academy, MNIT Jaipur in collaboration with the EC-Council aims to provide extensive training on Cyber Security concepts including risk analysis and mitigation, data security, cloud-based security, ethical hacking, etc. The course is designed by the top faculty at MNIT & Industry experts to help you gain relevant skills required by the Industry and land your dream job!
Learning Format
Online
Live Classes
7 Months
Career Services
by Intellipaat
Placement Assistance
by Intellipaat
EMI Starts
at ₹4999/month*
This PG certification course in Cyber Security and Ethical Hacking led by the faculty will help you strengthen your academic foundation and gain industry exposure. The skills that you will be learning in this course are all designed to meet the demands of the industry, thus paving the path for your career to grow successfully.
About E&ICT Academy MNIT, Jaipur
Electronics & ICT Academy MNIT, Jaipur (E&ICT MNIT, Jaipur) is an initiative supported by the Ministry of Electronics & Information Technology (MeitY), Govt of India. The courses provided by us lay an emphasis on bridging the gap between industry demand and academic approach to learning and provide a foundation to build yourRead More..
In this program, you will:
Achievements by MNIT:
About the EC-Council
This American organization offers education, training, and services on Cyber Security. The certification by the EC-Council validates the various cybersecurity skills that the learners will be trained in through the programme.
After this training, you will have the knowledge and skills to clear various Cyber Security Certifications, including the ones listed below:
Benefits for students from EC-Council
They are experts at reverse engineering and exploiting vulnerabilities and threats to offer insightful analysis and protect systems.
They perform settings analysis of operating systems and find problems in configurations and fix them.
These professionals monitor client systems and networks to detect and respond to attacks, vulnerabilities, and threats.
These experts are capable of performing user analysis to find trends, patterns, churn, segmentation, behavior, customer value, etc.
Ethical Hackers design security controls, standards, policies, and procedures for the organization’s security.
They oversee computer network systems to prevent potential security breaches as well as maintain system and security updates.
Skills to Master
Linux
Security and Risk Management
IoT Hacking
Cloud Computing
Cryptography
KPI
Footprinting and Reconnaissance
Vulnerability Analysis
System Hacking
Malware Threats
Sniffing
Social Engineering
Session Hijacking
Firewalls and Honeypots
Hacking Web Servers
RAID
Digital forensics
Tools to Master
Linux
2.1 Introduction to Ethical Hacking
2.2 Footprinting and Reconnaissance
2.3 Scanning Networks
2.4 Enumeration
2.5 Vulnerability Analysis
2.6 System Hacking
2.7 Malware Threats
2.8 Sniffing
2.9 Social Engineering
2.10 Denial-of-Service
2.11 Session Hijacking
2.12 Evading IDS, Firewalls, and Honeypots
2.13 Hacking Web Servers
2.14 Hacking Web Applications
2.15 SQL Injection
2.16 Hacking Wireless Networks
2.17 Hacking Mobile Platforms
2.18 IoT Hacking
2.19 Cloud Computing
2.20 Cryptography
3.1 Security and Risk Management
3.2 Asset Security
3.3 Security Architecture and Engineering
3.4 Communication and Network Security
3.5 Identity and Access Management (IAM)
3.6 Security Assessment and Testing
3.7 Security Operations
3.8 Software Development Security
4.1 Risk Management
4.2 Cryptography
4.3 Identity and Access Management
4.4 Tools of the Trade
4.5 Securing Individual Systems
4.6 The Basic LAN
4.7 Beyond the Basic LAN
4.8 Secure Protocols
4.9 Testing Your Infrastructure
4.10 Dealing with Incidents
5.1 Infrastructure Security: Network-level security, Host level security, Application-level security
5.2 Data security and Storage: Data privacy and security Issues, Jurisdictional issues raised by Data location
6.1 Access Control
6.2 Trust, Reputation, Risk
6.3 Authentication in cloud computing, Client access in cloud, Cloud contracting Model, Commercial and business considerations
Our Cyber Security and Ethical Hacking capstone project will allow you to implement your knowledge and skills gained during this training. Under the guidance of dedicated mentors, you will become capable of solving industry-grade problems through this project. Also, it will be the last step towards learning the course and showcasing your skills and knowledge in Ethical Hacking and Cyber Security to your future recruiters.
You will get to work on the following projects:
Practice 100+ Essential Tools
Designed by Industry Experts
Get Real-world Experience

Admission Details
The application process consists of three simple steps. An offer of admission will be made to selected candidates based on the feedback from the interview panel. The selected candidates will be notified over email and phone, and they can block their seats through the payment of the admission fee.
Submit Application
Tell us a bit about yourself and why you want to join this program
Application Review
An admission panel will shortlist candidates based on their application
Admission
Selected candidates will be notified within a week
Total Admission Fee
EMI Starts at
We partnered with financing companies to provide very competitive finance options at 0% interest rate
Financing Partners
![]()
Admissions close once the required number of students is enrolled for the upcoming cohort. Apply early to secure your seat.
| Date | Time | Batch Type | |
|---|---|---|---|
| Program Induction | 28th Sep 2025 | 08:00 PM IST | Weekend (Sat-Sun) |
| Regular Classes | 28th Sep 2025 | 08:00 PM IST | Weekend (Sat-Sun) |
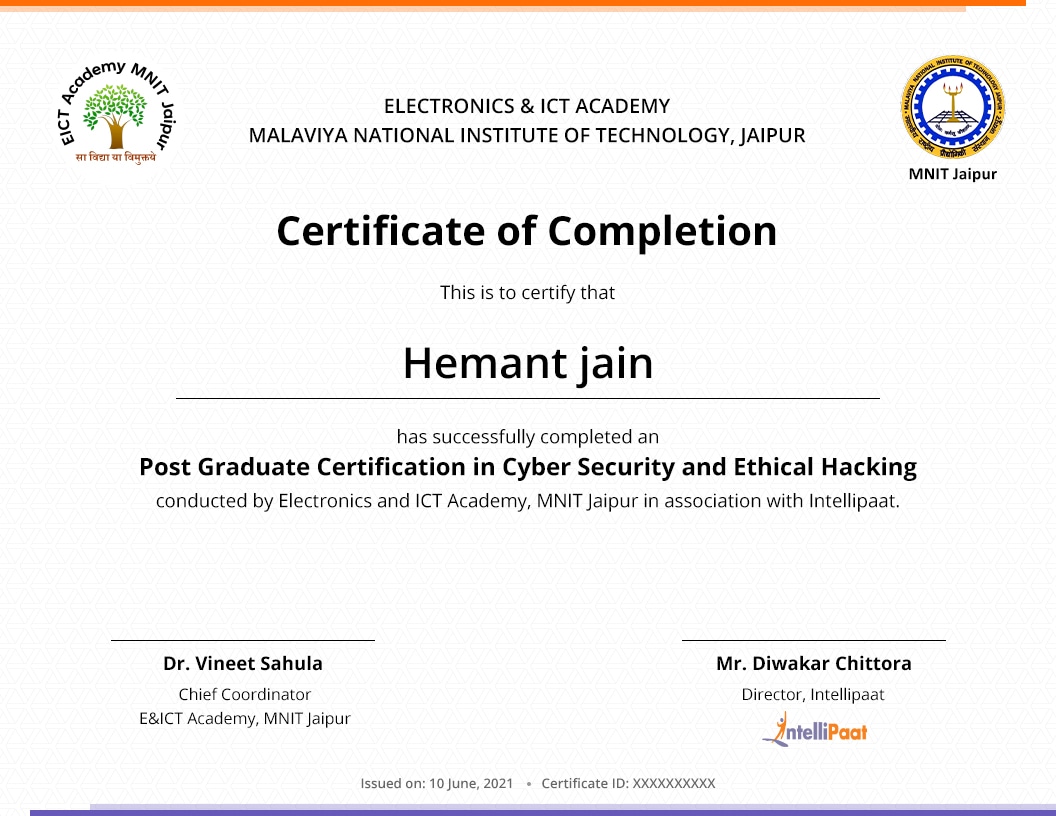
Our Cyber Security and Ethical Hacking online PG course will give you hands-on experience in mastering the concepts of Cyber Security and Ethical Hacking. You will master various topics like system hacking practices, Ethical Hacking enumeration, foot printing, and many more advanced concepts. After completing the course, you will be awarded PG certification from E&ICT MNIT, Jaipur.
As part of this course, you will work on several real-time projects and assignments that have high relevance in the corporate world. Upon completion of the course, you will be capable of applying for some of the best Cyber Security jobs in top MNCs around the world.
Intellipaat provides career services that include guaranteed interviews for all the learners enrolled in this course. EICT MNIT Jaipur is not responsible for the career services.
All our trainers are certified professionals in Cyber Security and Ethical Hacking from MNIT, Jaipur, and other popular industries with over 12 years of experience in the domain. They went through a rigorous process of selection before signing up as trainers with us for this course.
To get your PG certification in Cyber Security and Ethical Hacking, you have to first sign up for our PG course. You will need to complete the training program, along with all the projects and assignments that are part of the program. Once you meet all the requirements, you will receive your PG certification.
At Intellipaat, you will receive online training that will provide you with an in-depth understanding of all Cyber Security and Ethical Hacking concepts and you will get the chance to clear all your queries related to the training. Additionally, there are also session recordings available in case you need to refer them in the future or if you happen to miss any class.
The PG certification in Cyber Security and Ethical Hacking offers lifetime validity. You can use it to showcase your skills while applying for jobs in companies.
To get more information about this PG course, you can use the chat window that appears on the right or get in touch with our course advisors.
To be eligible for getting into the placement pool, the learner has to complete the course along with the submission of all projects and assignments. After this, he/she has to clear the Placement Readiness Test (PRT) to get into the placement pool and get access to our job portal as well as the career mentoring sessions.
Please note that the course fees is non-refundable and we will be at every step with you for your upskilling and professional growth needs.
Master Classes will be taken by the faculty. In case faculty is not available; the session will be taken by the other academicians from top NIT or IIT’s.
EC Council kit will be issued to those learners who have paid separately for the EC council kit. Please speak to the course advisor for the same.
Due to any reason you want to defer the batch or restart the classes in a new batch then you need to send the batch defer request on [email protected] and only 1 time batch defer request is allowed without any additional cost.
Learner can request for batch deferral to any of the cohorts starting in the next 3-6 months from the start date of the initial batch in which the student was originally enrolled for. Batch deferral requests are accepted only once but you should not have completed more than 20% of the program. If you want to defer the batch 2nd time then you need to pay batch defer fees which is equal to 10% of the total course fees paid for the program + Taxes.
Yes, Intellipaat certification is highly recognized in the industry. Our alumni work in more than 10,000 corporations and startups, which is a testament that our programs are industry-aligned and well-recognized. Additionally, the Intellipaat program is in partnership with the National Skill Development Corporation (NSDC), which further validates its credibility. Learners will get an NSDC certificate along with Intellipaat certificate for the programs they enroll in.
What is included in this course?
 Click to Zoom
Click to Zoom
 Click to Zoom
Click to Zoom